As readers might have noticed over the past few years, we Boggart Bloggers (especially the two cynical old gits whose careers primarily involved technology,) have a lot of doubts about 5G, the health risks, the threat to privacy, and the prospect of your ‘fridge spying on you for Nanny State all horrified us. And when we learned that governments were planning to adopt Chinese suppliers for the hardware and firmware, that was just beyond the pale. I mean, fucking China, the world’s biggest slave state? WTF?

from Wired
The world came together to build 5G. Now the next-generation wireless technology is pulling the world apart.
The latest version of the 5G technical specifications, expected Friday, adds features for connecting autonomous cars, intelligent factories, and internet-of-things devices to crazy fast 5G networks. The blueprints reflect a global effort to develop the technology, with contributions from more than a dozen companies from Europe, the US, and Asia.
And yet, 5G is also pulling nations apart—with the US and China anchoring the tug-of-war. Tensions between Washington and Beijing over trade, human rights, the handling of Covid-19, and Chinese misinformation are escalating global divisions around the deployment of 5G. A growing number of countries are aligning with either a Western or a Chinese version of the tech … Continue reading >>>
RELATED:
Facebook Bans All Content On Vaccine Awareness
Authored by Mike Adams via NaturalNews.com,
Just as we warned would happen, the tech giants are now moving aggressively to ban all speech that contradicts whatever “official” position is decided to be “the truth” by the corrupt establishment. This week, Facebook announced it would block all content on Facebook that questions the official dogma on vaccines,
German politician calls on facebook to abolish free speech
A German politician has given the clearest indication yet that the political elites of the free world are ideologically much closer to Adolf Hitler’s National Socialists than the social liberalism they claim to support. Free speech is the basis of all liberal democracy. Heiko Maas, the German justice minister has has written to the Facebook it removes “xenophobic and racist” anti-migrant posts from its website and apps., has written to the company to demand an urgent review of its policy over hate messages.
Free Speech Is Being Murdered By The Media And Left Wing Authoritarianism
Without free speech there is no democracy. Without democracy there is no freedom. But all over the developed world free speech is under attack from politically correct politics. It is time to start resisting, do not believe the propaganda published by mainstream media, question everything and make up your own mind. as The Buddha said, “Believe nothing you read or are told unless it agrees with your own experience and common sense.”
Farage Reckless Facing Rabid Left Wing Fanatics
Following the defection to UKIP of Conservative MP Mark Reckless, who yesterday shocked the media and political establishment (everyone else knew it was on the cards.) by announcing his switch from con to Kipper from the podium at the closing session of UKIP’s conference, the Kippers latest recruit and his new leader yesterday faced angry but ineffectual protests
Farage Reckless Facing Rabid Left Wing Fanatics
Following the defection to UKIP of Conservative MP Mark Reckless, who yesterday shocked the media and political establishment (everyone else knew it was on the cards.) by announcing his switch from con to Kipper from the podium at the closing session of UKIP’s conference, the Kippers latest recruit and his new leader yesterday faced angry but ineffectual protests
Obama administration ‘blocking’ information from the press
Uncovering information that should be available to the public has become increasingly difficult under the presidency of Barack Obama, an Associated Press bureau chief says. In some cases, it surpasses the secrecy of the George W. Bush administration. The White House’s penchant for secrecy does not just apply to the federal government, according to AP’s Washington bureau chief, Sally Buzbee.
Western Hypocrisy In Reporting News about Ukraine And Russia
The opening paragraph of a CNN report on the latest developments in the crisis in Ukraine illusrate perfectly the hypocrisy of Western media in the way they cast Russia as the danger to world peace and America as bringer of freedom and democracy. In fact in the crisis over the US attempt to draw Ukraine into NATO the positions taken by the USA abd Russias are the opposite of the 1962 Cuban Missile Crisis.
Scandal hit Rotherham ‘deleted abuse files’
In a move that puts them among the contenders for lying, self serving shits of the decade, but still in a league of their own un terms of complete and utter shittiness, it has emerged that the scum sucking scab lice of Rotherham Council’s controlling Labour group and the public servants they employed had deleted files in order to cover up their complicity in the blatant and systematic child abuse perpetrated under the noses of council officials.
Centralized power – the worst of all possible worlds
The centralization of power over the past few decades in nations of the developed world has led to the evolution of a sociopathic managerial class formed mainly from the old petite bourgoisie who have now gravitted to public sector careers where their delusions of social status and the unaccountability of office lead them to abuse such power as they have.
Kick Political Correctness Out Of Football
As another football versus politiocally correct authoritarianist brings ‘the beautiful game’ even further into disrepute, we wonder is it time to kick politically correct authoritarianism out of sport.
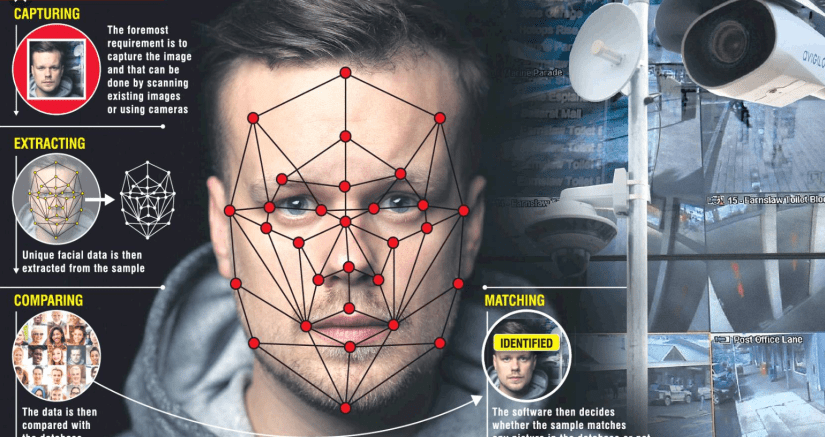
Intrusive Surveillance Technology, Internet control freaks and The Orwell-Huxley-Dick Dystiopianometer
Are privacy campaigners right to be worried about intrustive internet technology and the massive databases that log our behaviour and parse the data for patters that enable us to be targeted for advertising? Should we bee worried by surveillance or are those that raise doubts just scaremongering? The Orwell-huxley-Dick dystopianometer is rising.
So Who Is Anti – science? Those Who Question Climate Change Or Those Who Would Abolish Free Speech
It was looking as if the global warming scare was dead, then that Nazi shit Barack Obama, seeing his dream of being President Of The World slipping away, gave his science whores enough money to enable them to kick some life back into it. Now the “science” lobby, unable to put together an convinging argument against their challengers are demanding the abolition of free speech.
New World Order War On free Speech Comes To Britain – Guardian editor accused of treason
The right to free speech is under threat from intolerant, authoritarian elitists, call them The Illuminati, New World Order, Scientific Dictatorshgip, Global Elite, whatever. Their goal is absolute power and they know that while the right of free speech, the free press and free access to information exist they cannot succeed.
How academic debate is suppressed on science topics like Climate Change, GMOs, Pesticides and Toxicity of medicines
Intellectual intolerance and the supposed superiority of the scientific education have led not just to the politiciisation of science but to it’s being seduced by corporate money and political power. Science was ever fascism’s whore of course and the egos of scientists are easily bought. This has led to a very unhealthy emergence of dogmas and orthodoxies and an intolerance of the dissent that is essential if scientific research is to have any credibility.
Phobophobia – Fear Of Being called Phobic?
Homophobia is not fear of homosexuals but fear of thec same thing which does not make sense. Just as politically correct thinking uses the word bigot nonsensically so it’s accusations of phobia are irrational – as irrational as the groundless fear familiar to those who suffer the recognized medical conditions called phobias.
The Importance Of Free Speech And A Free Press
Politicians around the developed world including leaders of the two most powerful democracies, Barack Obama and David Cameron have been falling over themselves to join the attack on free speech. On subjects as diverse as climate…



Yet another ‘conspiracy theory’ has been proved true. (Picture: Sipa, AP images)
For years, conservatives, from bloggers and news sites to companies and political candidates have complained that Google, the dominant internet search engine, adjusts its search algorithms in order to manipulate results and ‘blank’ certain organisations and shades of opinion. Google has always denied the allegation charge, claiming there is no bias in the way that search results appear even though whistleblowing former employees have leaked documents showing it does, and tech analysts have offered statistical proof of malfeasance in listing search results.
According to the Wall Street Journal, (WSJ) Google’s protestations are as phoney as their search results.
The WSJ has published a report based on the findings of a major and far reaching investigation of Google’s search operation that involved interviews with hundred witnesses and examination of the tech corporation’s internal documents from the company. Investigators found that Google changed its search result listing algorithms 3,200 times last year (2018) with the aim of controlling what information users are offered links to. Much of that alteration was done in favor of promoting big business over small, as well as showing favor to big advertisers like eBay. But there were instances in which the company’s well known liberal and left wing political stance led to its weighting the algorithm against conservative and libertarian news and opinion too.
CNBC commented:
The company also blacklists one – issue campaign sites, as well as what it calls “hate sites,” (‘hate’ being whatever Google’s senior execs say it is, thus suggesting transgendered women are not ‘real’ women will be penalised, according to the investigation. They soft-pedal issues like abortion — which almost certainly hurts anti-abortion sites – and penalise Christian and Jewish religious sites while boosting sites promoting Islam.
Now a respected organisation such as the WSJ has recognised Google’s unethical corporate policy making, lack of credibility could quickly become huge problem for Google. Not only is it bad PR, but some Google executives may have perjured themselves in testimony before congressional committees.
National Review reports that Google also skews its search algorithms in other ways.
Ed Morrissey in PJ Media sums up the damage to democracy and independent businesses Google is doing.
When a powerful private company like Google, which through ill – considered political actions has been handed for too much influence over our access to information, trades neutrality for political influence and invites politicians to influence the way it does business, our many of our basic freedoms are put at risk .But Google’s parent company, Alphabet, like Facebook and other Silicon Valley behemoths, seems more intent on creating a global, cultural Marxist utopia than in doing honest business with the goal of making a modest profit. The founders and leaders of tese companies seem to believe they are above the law, and the fact that they can do something justifies doing it.
The WSJ investigation will no doubt give a boost to efforts by the EU competition commissioner, the governments of China, Japan, Russia, India and Philippines, and the 50 US state attorneys general currently looking into an anti-trust action against the tech giant. Perhaps Google’s fear of being broken up in accordance President Trump’s pledges to ‘drain the swamp’, or excluded from certain large and lucrative markets outside the US with will bring about a rethink of its policy, but I’m not betting on it.
More likely Google will continue to play dirty and try to defy attempts to apply some discipline to its activities which too often seem to stray outside the law and are always on that gery area on the edge of ethical behaviour.
RELATED POSTS:
Google wannabe Ministry Of Truth
Is Google governing the USA
Google algorithm is cheating us
Google omnibus
Facebook Steps Up Censorship, Bans Populist News Sites
Controlling Minds, Narratives and Elections: Google YouTube, Facebook & Twitter
The Internet Of Things